Eliminating SCA Noise using Dependency Usage Evidence
Table of Contents
A 3rd party dependency may be referenced in a package manifest such as requirements.txt or package-lock.json but not actually used in code. Vulnerabilities or other risks in such packages are not useful. Most SCA tools today lack the code context information preventing them from distinguishing between dependencies that are actually used in the codebase and those that are not. SafeDep Code Analysis framework augments vet, our free and open source tool with code context. This allows us to eliminate false positives and noise by considering the actual usage of a dependency in the codebase. In this article, we will look at how we can use dependency usage evidence to eliminate noise in SCA.
Getting Started
Ensure you have vet 1.9.2+ installed in your system. For help with installation, refer to the vet Installation Guide.
Create Code Analysis Database
Analyse your code base to create a code analysis database:
vet code scan --app /path/to/code --db /tmp/code.dbRun vet Scan with Code Analysis Database
Run vet scan with code analysis database to augment vet results with code context information:
vet scan -D /path/to/repository --code /tmp/code.dbDemo
- sca
- nextgen-sca
- code-analysis
- guide
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
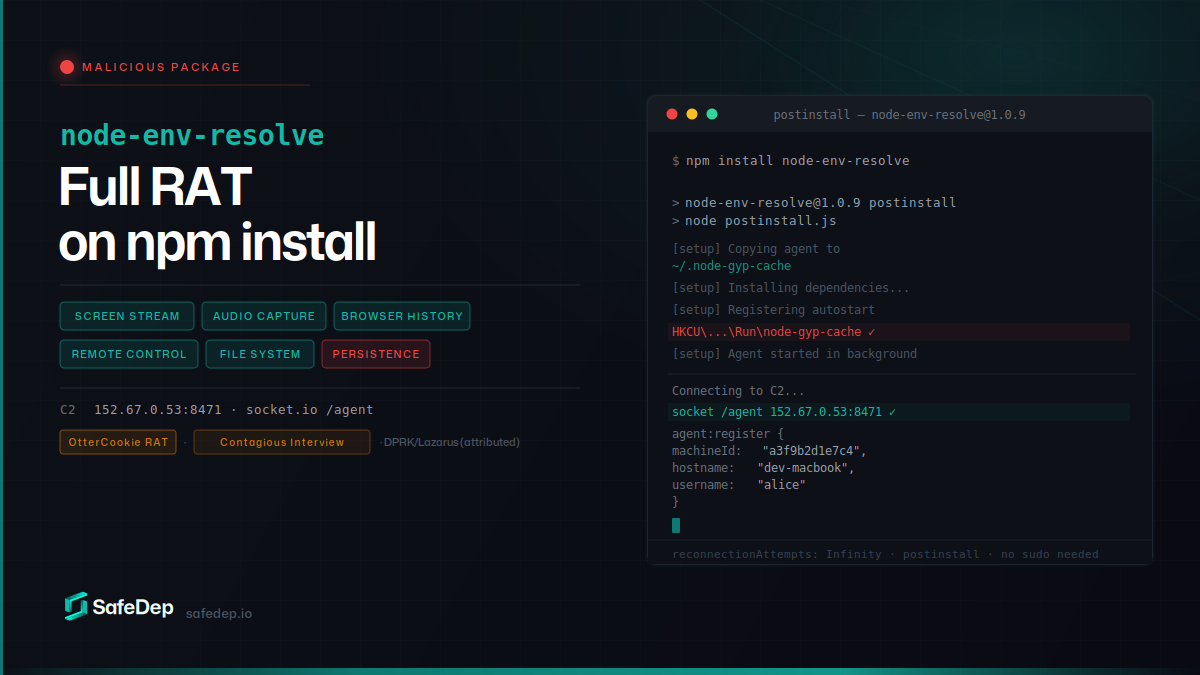
node-env-resolve: npm Package Installs a Full RAT
node-env-resolve is a malicious npm package that installs a full-featured remote access trojan on developer machines. The RAT streams screens, captures audio, steals browser history, and gives full...
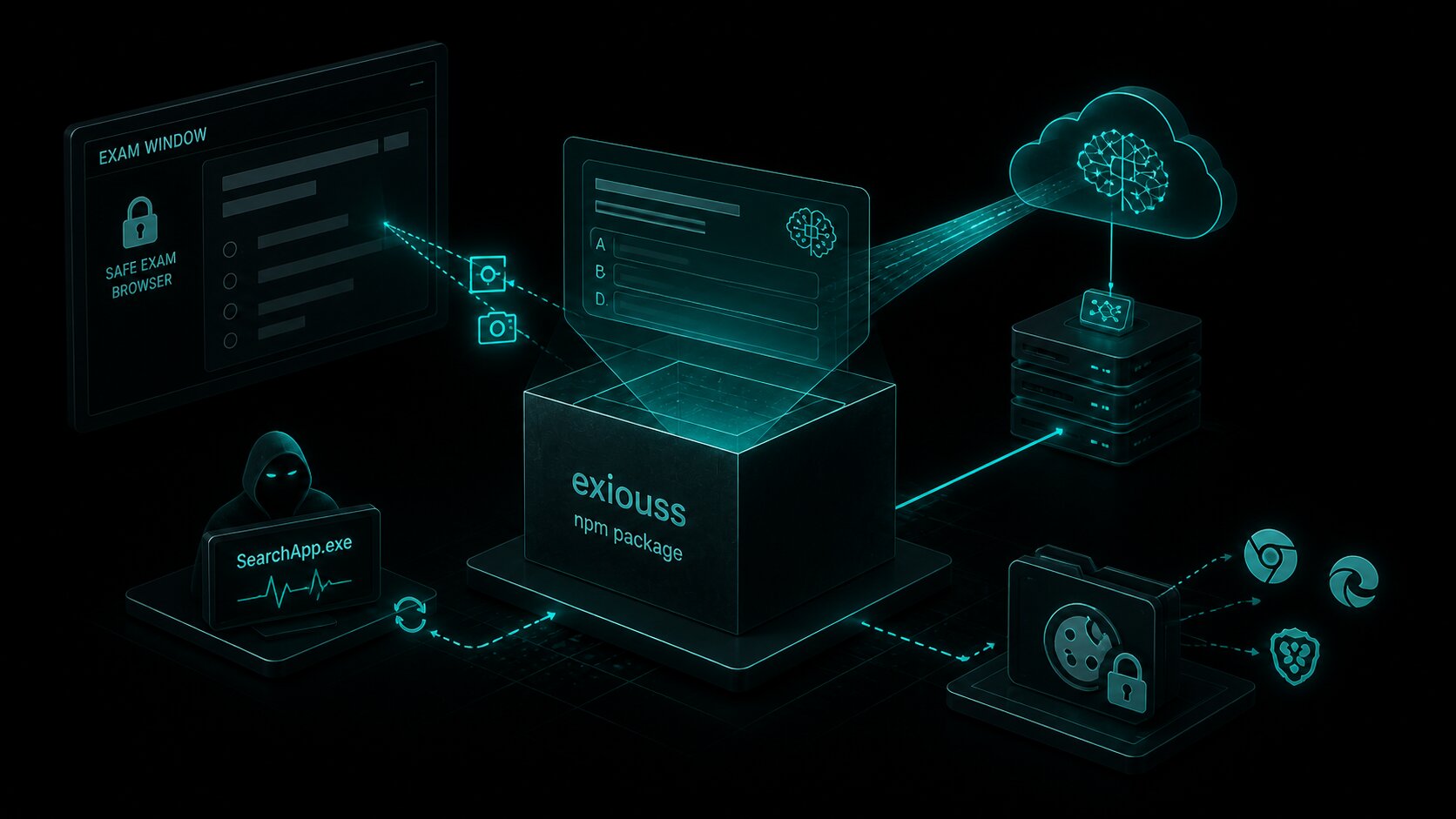
exiouss: Cookie Stealer Bundled in npm Exam Cheat
exiouss on npm is the latest package from the loltestpad campaign — the same attacker who published the ixpresso-core Windows RAT in April. It bundles a dormant ChatGPT cookie stealer alongside an AI...
common-tg-service: 502 npm Versions Hijack Telegram
common-tg-service ships 502 npm versions of a Telegram account-takeover framework with hardcoded 2FA credentials, IMAP-based code harvesting, and forced session eviction. Its companion package...

PyTorch Lightning Compromised: Shai-Hulud Worm Reaches PyPI
PyPI yanked PyTorch Lightning versions 2.6.2 and 2.6.3 after both embedded a two-stage credential-stealing payload. Any import of the library spawns an 11MB obfuscated JavaScript worm identical to...
Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
