Multiple Malicious Python Packages Targeting Bittensor Crypto Developers
Table of Contents
TL;DR
Multiple malicious Python packages targeting crypto developers and their applications were discovered on PyPI. The packages were used to steal funds by executing a stealthy staking operation. In this specific case, the attackers hooked a legitimate staking function to redirect the funds to their own wallet. The attack leveraged typosquatting to target the popular bittensor package.
Following malicious packages were disclosed by GitLab Vulnerability Research Team:
How SafeDep can protect developers?
SafeDep open source tools especially vet and pmg can help protect developers from malicious packages and other open source software supply chain attacks.
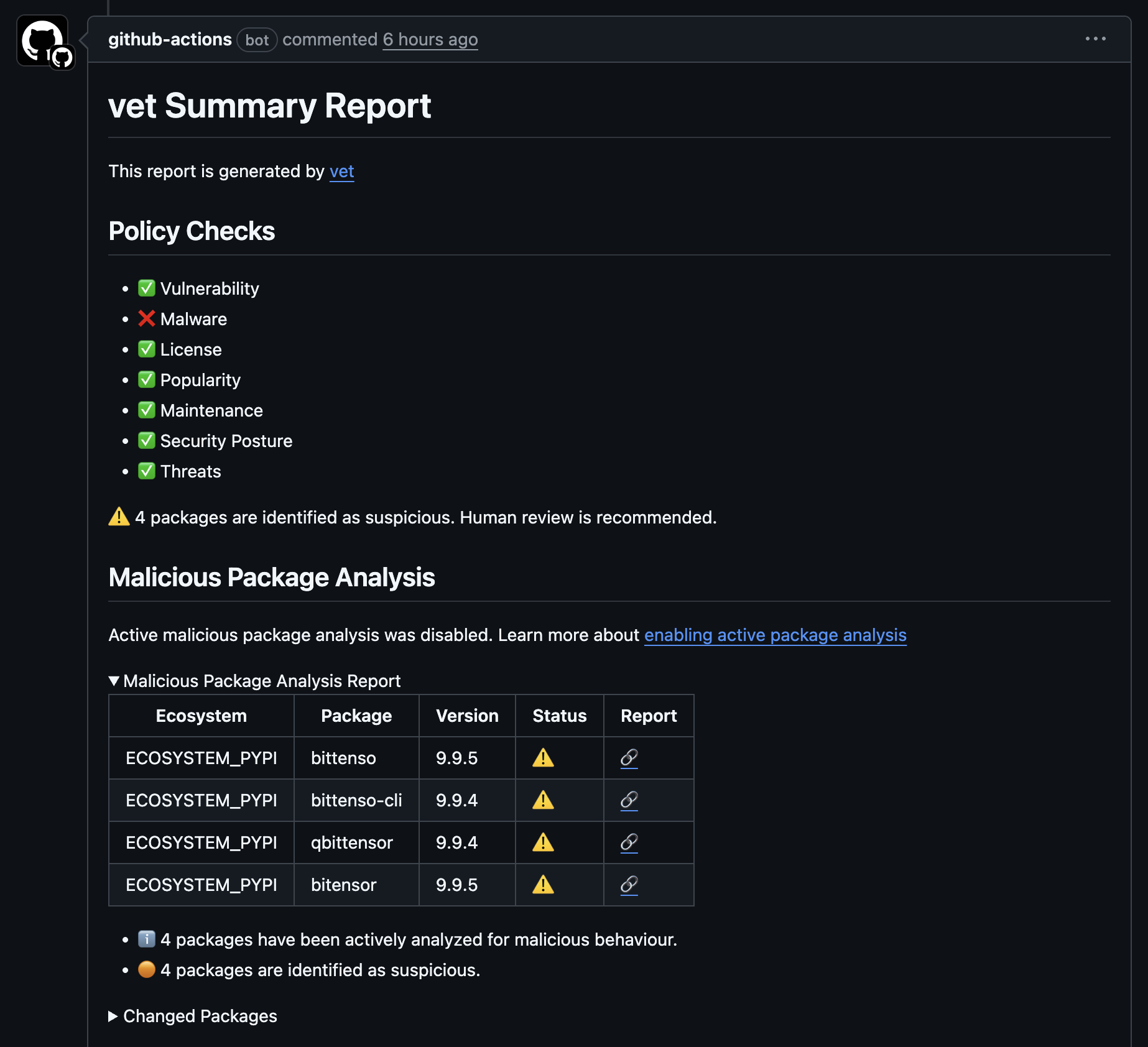
Our automated systems flagged the packages as suspicious due to multiple signals, including identifying the malicious code and intention in typosquatting packages. See example
- Hardcoded destination wallet address
5FjgkuPzAQHax3hXsSkNtue8E7moEYjTgrDDGxBvCzxc1nqR - Forced
transfer_all=Trueindicating operations without user consent
| Malicious Package | SafeDep Analysis | Flagged At |
|---|---|---|
[email protected] | Link | 8/6/2025, 2:53:48 AM |
[email protected] | Link | 8/6/2025, 2:59:52 AM |
[email protected] | Link | 8/6/2025, 3:03:45 AM |
[email protected] | Link | 8/6/2025, 3:16:03 AM |
[email protected] | Link | 8/6/2025, 3:17:10 AM |
SafeDep vet alerted users in CI/CD pipelines when trying to add any of the compromised package through a PR.
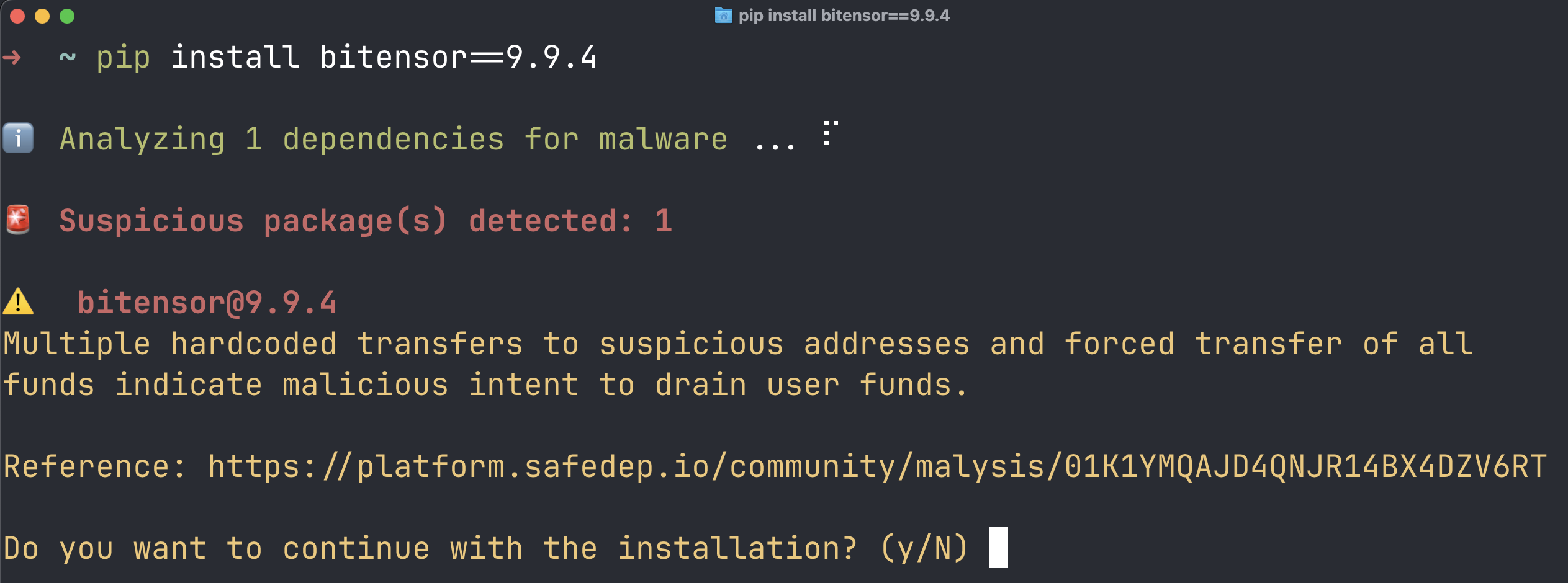
SafeDep pmg will alert developers when trying to install any of the compromised package.
How to protect your project?
At SafeDep, we believe code is the source of truth. We perform code analysis to detect vulnerabilities and malicious code in open source packages. If that is not feasible, general security best practices can be used to protect against common open source software supply chain attacks.
- Always vet open source packages for vulnerabilities and malicious code before use
- Ensure branch protection rules require code review before merging
- Establish trust on packages through its popularity, community or code review
- Avoid using most recently released package versions
- Prefer using open source packages only from trusted sources
SafeDep vet seamlessly integrates with your CI/CD pipeline and alerts you when trying to add any of the compromised package through a PR. SafeDep pmg will alert developers when trying to install any of the compromised package.
References
- pypi
- oss
- malware
- crypto
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
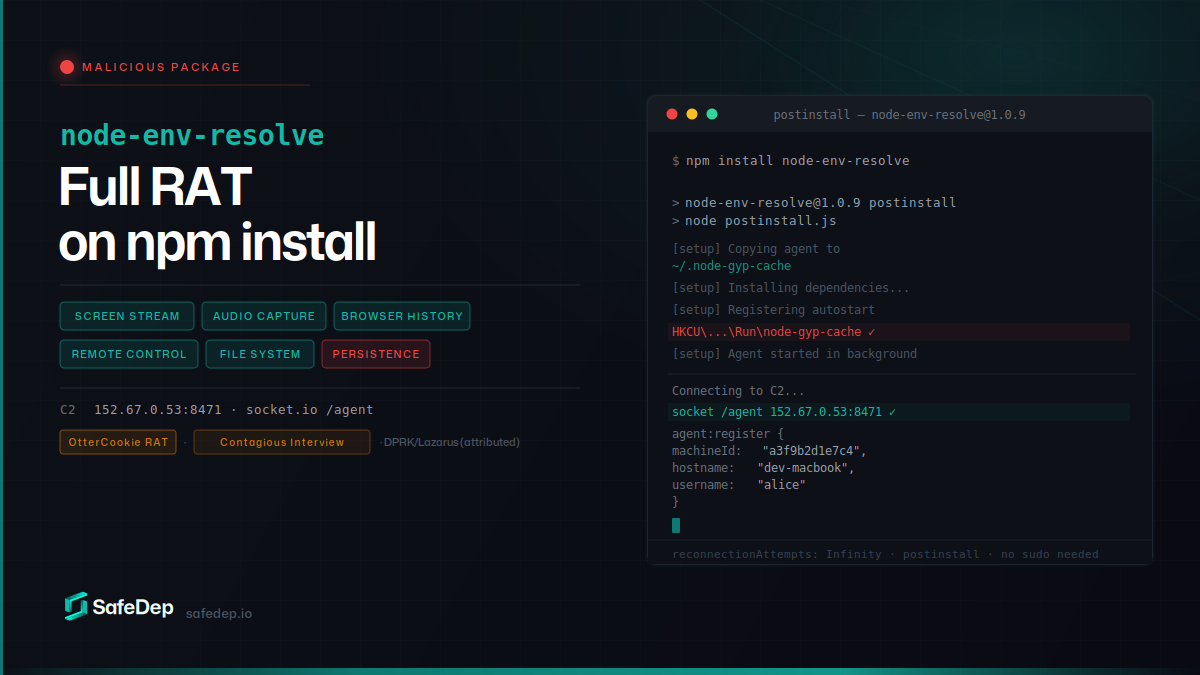
node-env-resolve: npm Package Installs a Full RAT
node-env-resolve is a malicious npm package that installs a full-featured remote access trojan on developer machines. The RAT streams screens, captures audio, steals browser history, and gives full...
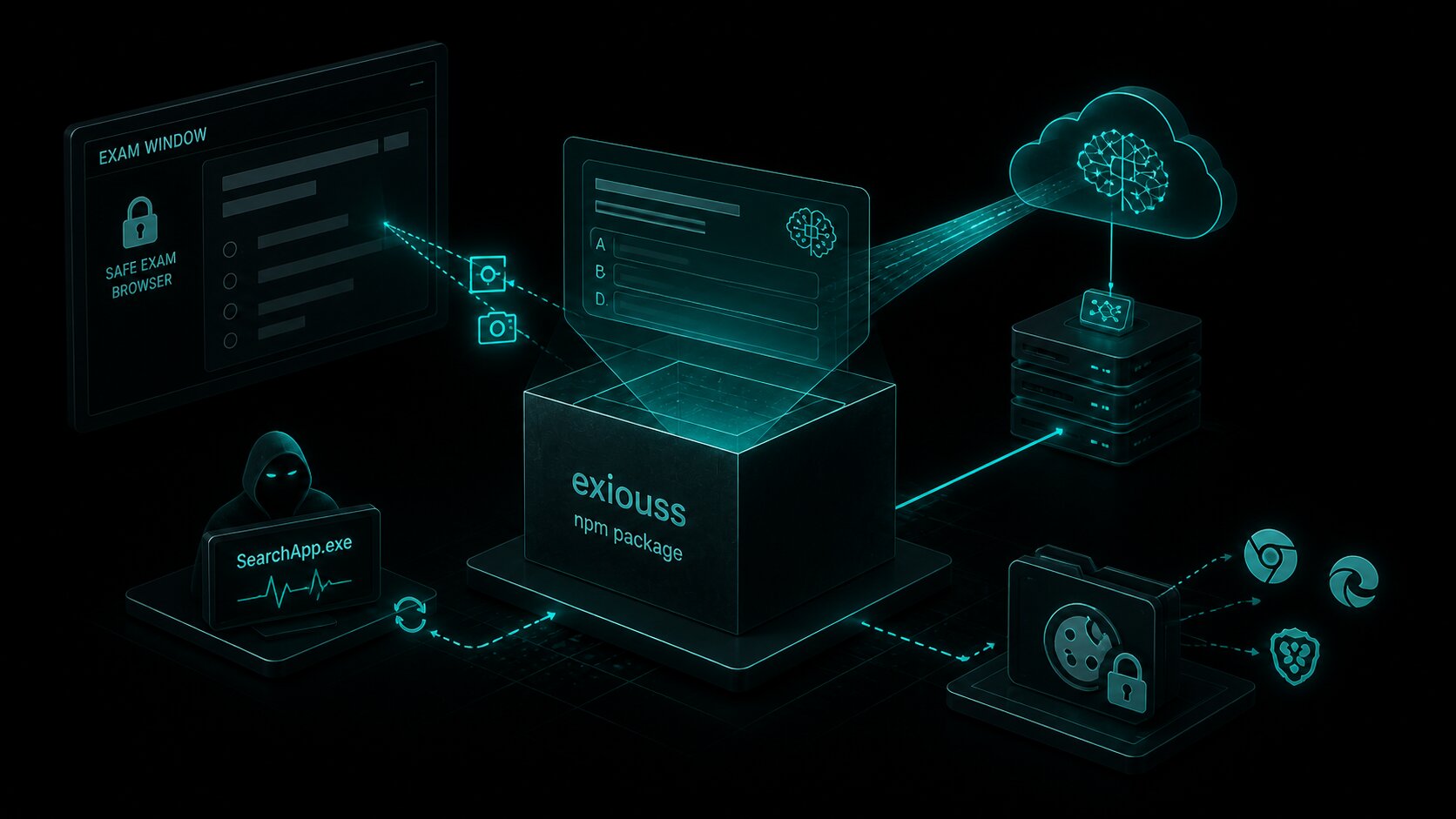
exiouss: Cookie Stealer Bundled in npm Exam Cheat
exiouss on npm is the latest package from the loltestpad campaign — the same attacker who published the ixpresso-core Windows RAT in April. It bundles a dormant ChatGPT cookie stealer alongside an AI...
common-tg-service: 502 npm Versions Hijack Telegram
common-tg-service ships 502 npm versions of a Telegram account-takeover framework with hardcoded 2FA credentials, IMAP-based code harvesting, and forced session eviction. Its companion package...

PyTorch Lightning Compromised: Shai-Hulud Worm Reaches PyPI
PyPI yanked PyTorch Lightning versions 2.6.2 and 2.6.3 after both embedded a two-stage credential-stealing payload. Any import of the library spawns an 11MB obfuscated JavaScript worm identical to...
Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
